The COM
Content Warning: This page contains information regarding child sexual exploitation, harm, and violence, which may be distressing. Below, you will find an introduction to ‘The Com’ along with warning signs and resource guides. A second section provides in-depth research and further insights for those seeking more detailed information.
What is The Com?
"The Com" (or "The Community") is a vast, interconnected network of digital spaces spanning both mainstream and encrypted platforms. This ecosystem consists of overlapping servers and forums that, while distinct, share a unified culture centered on anti-social behavior. Within this ecosystem, sub groups and members collaborate and compete, creating a volatile environment where activities frequently escalate into criminal behaviour and violent extremism.
Who:
Victims and Perpetrators are male and females, typically aged between 11 and 24 years. Some victims have been as young as 8 years old and many victims can become perpetrators. Example sub-groups: 764, Harm Nation, No Lives Matter (NLM), CVTIST, Leak Society, Kasker, 7997, and H3ll.
How:
Perpetrators use popular games like Minecraft and Robolox, or other online mainstream spaces to access vulnerable individuals.
INITIAL CONTACT:
Individuals are targeted in mainstream or gaming environments such as Minecraft or Roblox or on TikTok and Snapchat and other mainstream platforms like Pinterest or Reddit.
DIRECT MESSAGE:
Initiate contact by sending direct messages to the individual while playing
PLATFORM SHIFT:
Core tactic is to move the targeted individual to external platform like Discord or Telegram.
ESCALATION:
Once moved to other platforms, interactions become coercive, sexualised or violent.
This process allows them to bypass safety features and content moderation built into children’s video games and platforms. By isolating their victims, these actors can more easily blackmail / extort the victim into acts of self-harm, animal cruelty, or sexually explicit acts. These activities are the leverage used to exploit the targeted individual, encouraging them to commit acts and/ or victimise others. More information and warning sign resources are below, signs can include self-harm, harming others, and hurting pets.


AI Image


If you have concerns about a child and their involvement with the Com, seek help early and stay calm.
Discussion Guide for Parents and Caregivers (link)
Keep It Real Online - DIA New Zealand. (link)
Europol Advice For Parents re the Com ( link)
Know the Signs NZSIS (pdf)
Spotting the Signs: Recognising and Responding to Subcultures of Nihilistic Violence (pdf)
Decoding Your Teen’s Hidden Online Lingo: A Parent’s Guide (pdf)
NZ Guide to Digital Family Safety Apps
Netsafe New Zealand (link)
Resources for Educators (Public Safety Canada) (link)
Help and Advice:
NZ Police 111 Emergency or 105.
Victim Support 0800 842 846
Lifeline 0800 543 354 or text HELP to 4357
Youthline 0800 376 633 or text 234
Online Safety Advice: Department of Internal Affairs.
Rural Support Helpline 0800 787 254
Rainbow Youth (09) 3764155
OUTLine 0800 688 5463
Safe to Talk 0800 044 334 or text 4334
Report Harmful Content Department of Internal Affairs.
Section Two
Content Warning: This content contains information regarding child sexual exploitation, harm, and violence, which may be distressing.
Audio - Ai discussion based on 20 studies/analysis & official reports on ‘The Com’. Time: 18 minutes All sources are listed at the bottom of this page.
The COM Ecosystem
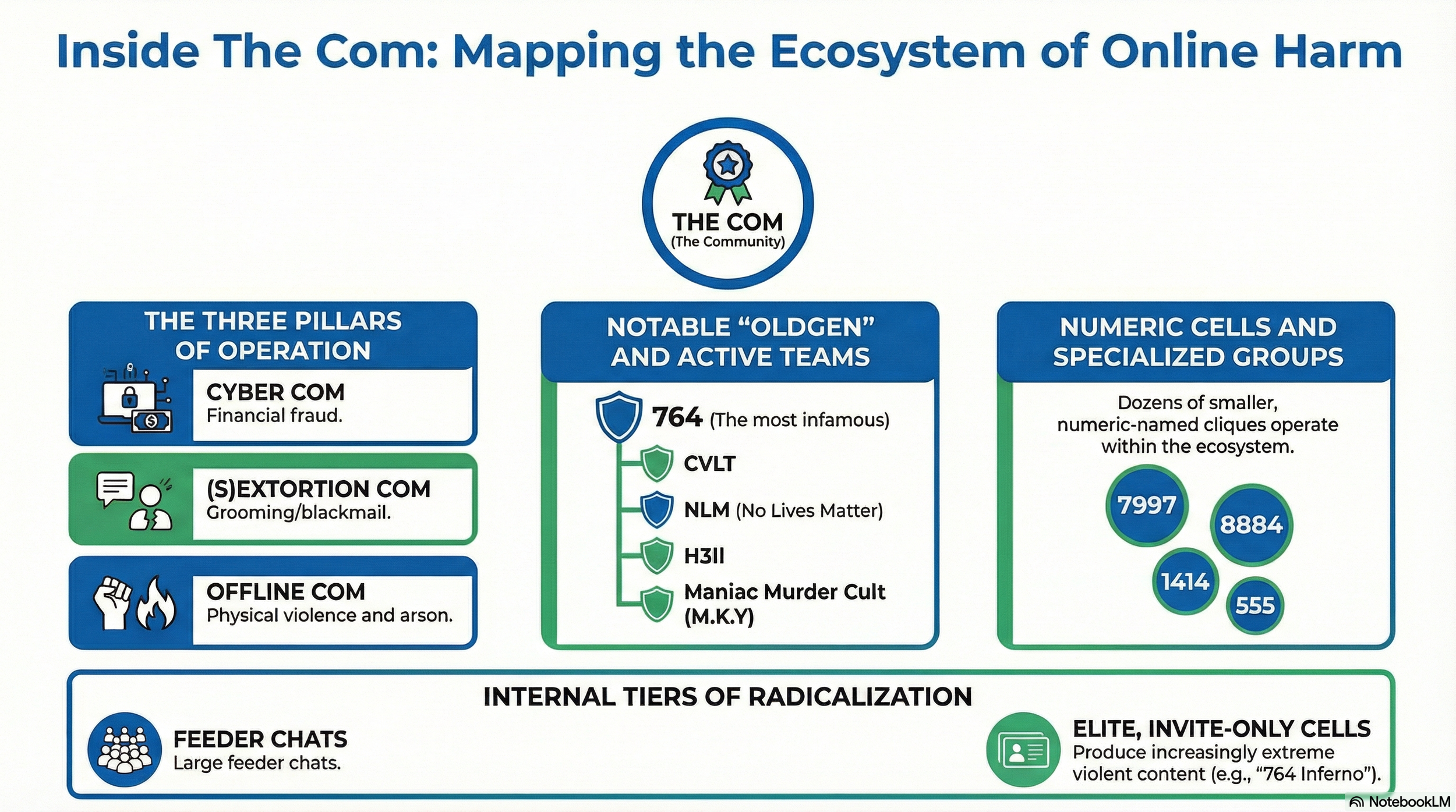
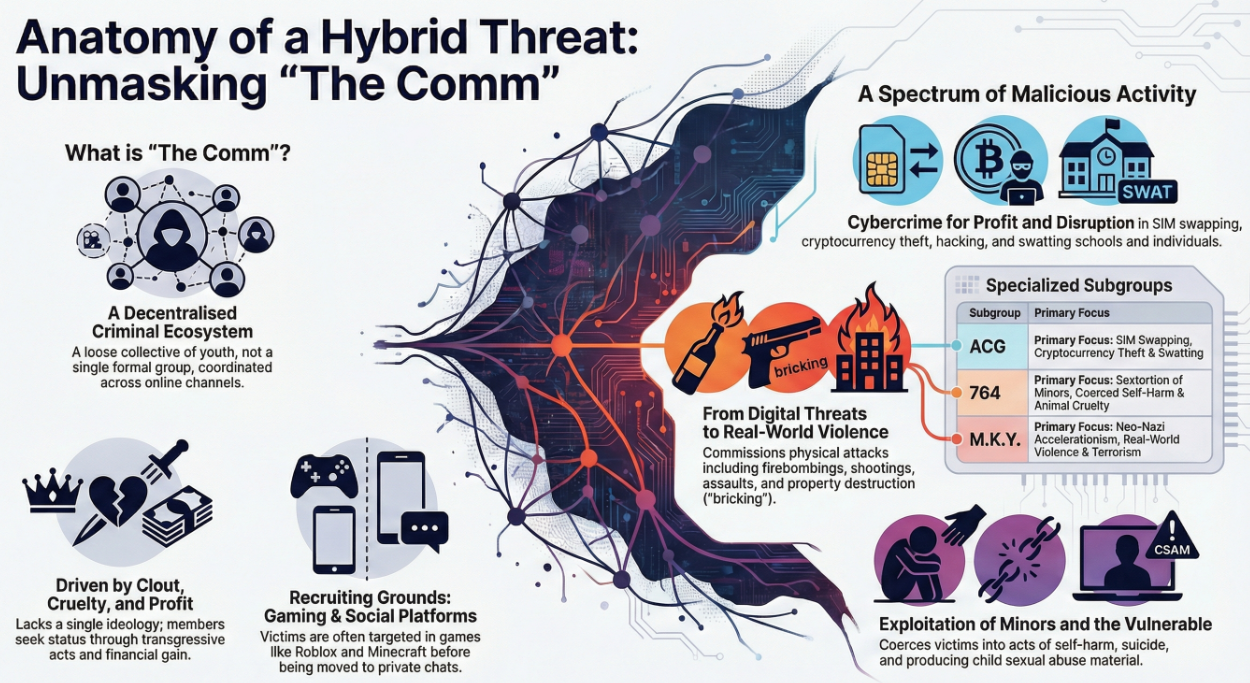
As well as the names above other subgroups exist but branding can change or new subgroups emerge quickly. Other numerical codes are used as group names include 2992, 6996, 545, 404. and 303. These groups often use symbols from Neo-Nazi or Satanic extremist groups, however this can be for shock value and intimidation rather than a true belief in what they stand for. These subgroups tend operate from three pillars depending on their motivations: Cyber com, Sextortion Com, and Offline com but there can be overlap.
Slang and Terms : (examples)
Lorebooks: .
This refers to films or files created by abusers that contain sexually explicit content, self-harm images, and documentation of a victim’s extortion. These are circulated among the group to gain “clout” and are used as blackmail to exert further control over the victim.
Fansigning:
A term for when victims are forced or manipulated into writing or cutting specific numbers, letters, symbols, or their abuser’s screen name cirectly into their skin.
Bricking:
A term for throwing a brick through a window of a target’s vehicle or home, a acto of real-world violence encouraged or commissioned. Can be an initiation or intimidation.
Murder Points:
A scoring system used by the M.K.Y subgroup to evaluate the productivity of its members, rewarding them for criminal and/or brutal acts.
Sim Swapping
Telecomm provider is tricked into transferring your phone number to their device.
Swatting:
Calling in a fake emergency that prompts a armed police response to the victim’s home. Includes bomb threats to schools. Can be used to threaten a victim into compliance
Doxxing:
Obtaining and publishing personal idenitifying information online.
Edgelord:
Some who deliberately posts shocking, offensive, or nihilistic content online to appear cool, or to provoke a reaction.
Saints:
Glorification of mass murderers , especially school shooters.
Nihilism and Terror: How M.K.Y is Redefining Terrorism, Recruitment, and Mass Violence. Marc-Andre Argentino, Barrett Gay, and Matt Bastin. CTC Sentinel September 2024
No Future, Only Violence: Unpacking the Propaganda of No Lives Matter (NLM) and 764. A Magnus. (Masters Thesis) 2025
Ideological and nihilistic violence in adolescents referred to a specialized clinic for violent extremism. C Rousseau, D Miconi, C Ngov & G Hassan. Canadian Journal of Criminology and Criminal Justice. Vol 67:2 (2025):30-48
Understanding the Relationship Between 764 and the Com Network. Marc-Andre Argentino & Peter Smith
Cutecore: The Soft Look of the Com Network. Marc-Andre Argentino
Nihilistic violent extremist networks recruit vulnerable people - and our youth need support. Kawser Almond.
764: In Depth Review and Analysis of 764 and other numbered online nihilistic-acceleration extremist movements targeting children. 2025
Young People and Violent Extremism - Five Eyes Bulletin -Call for Collective Action.
Weaponised Loneliness - Critical Harm Briefing , Resolver January 2026
Fury & Void: Legal Pathways to Counter 764. Tanya Mehra and Menso Hartgers. ICCT Policy Brief. 29 Oct 2025
Stop Criminal Networks from Recruiting Youngsters - Advice for Parents. Europol. 20 Apr 2025
Violent Online Networks Target Vulnerable and Underage Populations Across the United States and Around the Globe. Alert Number I-030625-PSA. FBI. 6 March 2025.
Hybrid Extremism and Nihilistic Violence. ISD Feb 2026
Leaders of 764 Arrested and Charged for Operating Global Child Exploitation Enterprise. FBI. 2025
Hawkes Bay Man named as planner of mass killing & distributor of child sexual exploitation material. RNZ 27 Feb 2026
Gamifying Harm: The Com. Sky News
Is Roblox getting Worse ? Wired. Aug 2025
Project Compass - Europol - Global Efforts re the Com
True Crime Community associated with tragedy, highlights nihilistic violence’s threat. ISD Jan 2026
Recent US Perpetrators indicate shift in extremist landscape, rise in nihlistic violence. ISD Dec 2025.
Memetic Violence: How the True Crime Community generates its own. ISD. Oct 2025.
ISD Analysts warn against overapplying the label of Nihilistic Violence. Steven Rai July 2025.
764 Networks of Harm - A Victim - Centric Info Resource. ISD
Com Networks Alert. NCA - National Crime Agency
“The Comm - The Group Linked to a Nationwide Swatting Rampage 31 May 2023 The Vice
Canadian Community Centre Vandalism Names Violent International Neo-Nazi Group. 7 Jan 2025. AntiHateCA
Europol-led crackdown on The Com hackers leads to 30 arrests. Sergiu Gatlan 27 Feb 2026
Nihilistic violence adds to South East Asia’s Youth Radicalisation Concerns. Hariz Baharudin Feb 2026